In today’s interconnected and data-driven world, the confidentiality, integrity, and availability of sensitive information form the lifeblood of most modern organizations. The stakes are higher than ever, whether it’s personal data, financial transactions, intellectual property, or trade secrets. As more enterprises move to digitize their operations and shift core business processes online, the onus of safeguarding this plethora of digital assets has become paramount. Yet, with the move to the digital realm, the complexities of data protection have increased manifold. Threat vectors, ranging from sophisticated cyber-attacks, data breaches, insider threats, and ransomware, to name just a few, are ever-evolving. The expanding digital landscape, characterized by cloud infrastructures, remote workforces, and interconnected devices, only adds to the challenge. Thus, for organizations that handle sensitive information, understanding the fundamentals of digital security becomes non-negotiable.
However, addressing this challenge isn’t solely about implementing the latest security tool or adopting the newest encryption algorithm. It’s about establishing a comprehensive, multi-faceted approach that proactively understands and responds to threats, keeps pace with technological advancements, and recognizes the human element in data protection.
A Culture of Security Awareness

The foundation of any robust security posture begins with its people. Employees, from the CEO to the newest recruit, play a critical role in maintaining security protocols. Every organization member must understand the importance of data protection, the risks involved, and their role in the larger security framework. Regular training sessions, workshops, and awareness campaigns can ensure that the staff is up-to-date with the latest security protocols, understands the ramifications of a breach, and is equipped to recognize and report potential threats. A well-informed workforce becomes the first line of defense, capable of mitigating risks before they escalate.
Embracing Cloud Infrastructures Wisely
The transition to cloud-based operations has created a new paradigm of challenges and opportunities. Cloud platforms offer scalability, flexibility, and cost-effectiveness. However, they also introduce new security concerns. When mastering cloud security, organizations must ensure that data stored in the cloud is encrypted at rest and in transit. This ensures that the data remains unintelligible even if there’s unauthorized access. Additionally, robust access controls and multi-factor authentication can deter unauthorized access. Collaborating with cloud providers to understand shared responsibilities in security ensures both parties play their roles effectively, thus ensuring a more fortified environment.
Data Classification and Access Control
Not all data is created equal. Organizations often possess a mix of public information, operational data, and highly sensitive confidential assets. By classifying data based on sensitivity and criticality, organizations can allocate resources and protections where they’re most needed. Access control ties closely with data classification. By granting access rights based on roles within the organization, one ensures that sensitive information is only accessible to those with a legitimate need. This minimizes potential exposure and reduces the attack surface.
Adherence to Established Standards: NIST 800-37
In the vast realm of digital security, it’s vital to have standardized guidelines and frameworks that offer clarity and direction. NIST 800-37 is one such essential guide that provides a risk management framework for organizations. By following the NIST 800-37 guidelines, organizations can identify, assess, and prioritize risks, design robust controls, and monitor and review their effectiveness over time. What makes this framework especially beneficial is its holistic approach that encompasses both the technological and human aspects of data protection. Its positive impact on organizations is unparalleled. Adopting NIST 800-37 demonstrates a commitment to upholding the highest standards of security and reassures stakeholders, clients, and partners of the organization’s dedication to safeguarding sensitive information.
Proactive Threat Intelligence

The cyber-threat landscape is constantly evolving. To stay ahead, organizations need to adopt a proactive stance, continually seeking out potential threats, understanding emerging attack vectors, and adapting defenses accordingly. Investing in threat intelligence platforms and collaborating with industry peers can provide valuable insights into current threats. Having this intelligence allows for timely countermeasures, ensuring that defenses are always a step ahead.
Regular Audits and Penetration Testing
No security posture is foolproof. Regular audits and penetration testing provide a reality check, revealing vulnerabilities and gaps in the existing framework. By simulating real-world attacks, penetration testing offers a practical assessment of how defenses would hold up under a genuine threat. Regular reviews ensure that systems are updated, redundancies are eliminated, and resources are allocated effectively.
In a world where data is power, safeguarding sensitive information is not just a necessity but a responsibility. Organizations must champion a holistic approach, from fostering a culture of awareness to adhering to standards like NIST 800-37. The journey towards comprehensive digital security is intricate and ongoing, but with diligence, commitment, and the right strategies, it is a challenge that can be surmounted.
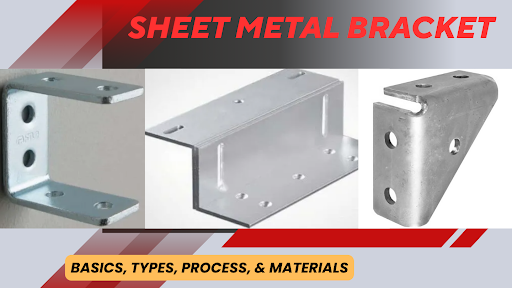
Sheet Metal Bracket: Basics, Types, Process, & Materials

Guide to Pre-Lubricated Switches for Backlit Gaming Keyboards

How Telegram Helps Online Communities Grow



