Understanding Cyber Security Courses: A Comprehensive Overview

Businesses today depend on data to make decisions. In the face of increasing competition, customers saving their personal information online, trusting the company, and with the rampant instances of cyber crimes, there arises a need to secure data from cyber threats. The discipline that studies how computer networks and systems can be protected such that the data can be prevented from such theft or harm is called Cyber security.
Identifying the need to stop cyber crimes, cyber security courses teach students to identify digital exploitation and system vulnerabilities and prevent damage, such as loss of data and loss of money due to the system being infected by viruses. The students are also taught how to avoid such attacks and the implementation techniques for preventing such attacks and counter-attacks against cyber threats. Companies such as Apple, General Motors, Federal Reserve Bank of New York, Cisco, Capital One, Intel, Boeing, Northrop Grumman, Lockheed Martin, Patient First, and many more are looking for professionals who can save data from such losses. Depending upon the role and expertise, the annual median salary of a cybersecurity professional can range between USD 52,700 to USD 1,20,600.
What Is the Role of a Cybersecurity Specialist?
The job of Cybersecurity specialists is to secure information systems by monitoring, detecting, investigating, and responding to security events. They undertake the following activities to achieve this objective:
- They anticipate future threats and provide consultation to companies on how they can implement security controls to prevent security breaches.
- They develop and execute security measures and policies to prevent data breaches and unauthorized system access and to ensure protection against threats such as viruses, spyware, worms, and so on.
- Cyber security specialists conduct audits, which is a term referring to a comprehensive review of an organization’s IT infrastructure. This is done to identify if there exist security issues within a system that can lead to data breaches. The review must ensure that the organization’s data, operations, network, and security system are secured.
- Most organizations respond to cyber security incidents by outlining steps and procedures in case of occurrences of data breaches. At first, one should recognize the threat and determine the severity of the threat. Next, they should contain and take measures to eradicate the threat before it causes further damage. In the end, for post-recovery, one should review the lessons learned and accordingly adjust the security controls.
- Cyber security experts are expected to be updated regarding new attack vectors, recent high-impact security incidents, and any policies released in regard to this domain. Given that hackers are always on the lookout for new ways to breach system security, staying abreast of recent updates is an absolute necessity.
- Experts supervise network activity. They investigate the situation if they find any potential sign of external interference. If necessary, they can also perform a forensic analysis to identify the source of the threat, if the source is still present, and the turn of events that led to the outcome.
Other job roles that a cyber security graduate can take up are tabulated as follows:
| Chief Information Security Officer | Forensic Expert |
| Security Code Auditor | Penetration Tester |
| Security Auditor | Cryptographer |
| Security Administrator | Security Consultant |
| Vulnerability Accessor | Security Manager |
| Security Software Developer | Security Analyst |
| Security Architect | Security Engineer |
| Incident Responder |
Educational Eligibility
You have the option to do an undergraduate, postgraduate, or online course in cybersecurity. Different colleges in India have different eligibility criteria depending on the courses you want to avail of. The basic eligibility criteria for the courses of these levels are as follows:
Undergraduate Degree Course – The student must have passed 10+2 in the Science stream from a recognized board
Postgraduate Course – The student must have:
- Passed their graduation in Cyber Security Computer Science, or a related field with 3 or a higher GPA (4-point scale) or 8.75 GPA (10-point scale) or 83% for the last two years of undergraduate studies.
- 1-2 years of studies in calculus and other areas of Mathematics, such as linear algebra, differential equations, and so on
- Knowledge of Computer Science such as programming, computer architecture, data structures, and so on
- English proficiency. Passing TOEFL/IELTS exams with the score as specified by the institution is a must for international students.
Some of the postgraduate course options that students can avail of in the USA are:
- MS in CyberSecurity
- MS in Information Assurance
- MS in Computer Science with Cybersecurity specialization
- MS in Information Technology
Online Course – The student must have a basic understanding of using the internet and operating systems and know how to download and install the software. A strong will to create a career in cybersecurity goes a long way.
Listed below are some universities from which students can pursue cybersecurity courses in the United States:
- University of California Berkeley
- University of Maryland
- University of Delaware
- George Washington University
- Mercyhurst University
- New Jersey Institute of Technology
- Syracuse University
- Tufts University
- Stevens Institute of Technology
- University of Tampa
Scholarships for Cybersecurity Post Graduation in the USA
If you are a non-native of the USA and are going there only to pursue higher education, expect to pay a wholesome amount combining the cost of living and the course fee. One way that you can save some pennies is through scholarships. Here are some of the grants that international students can avail of.
| Name of the Scholarship | Amount (in INR) |
| Hubert H. Humphrey Fellowship | Variable |
| Aga Khan Foundation Scholarship | 50% grant and 50% bank loan |
| Inlakhs Shivdasani Foundation Program | Varies |
| Women Techmaker’s Scholarship | 7.81 Lakhs |
| Stokes Educational Scholarship | 23.44 Lakhs |
| NSF CyberCorps Scholarship for Service | 39.07 Lakhs |
Conclusion
Cyber security is promising. However, before you zero down the choice for career and higher education, it’s best to identify your suitability with the domain. To be successful in this field, the expert should be strong in programming, analytical, security, and problem-solving skills. Know that skills can be built over time. So, if you are weak in a certain skill, work on developing it to ensure a promising future.

What are the Most Popular Online Casino Games?

Security Guard vs Security Officer: Choosing Roles in Different Risk Environments
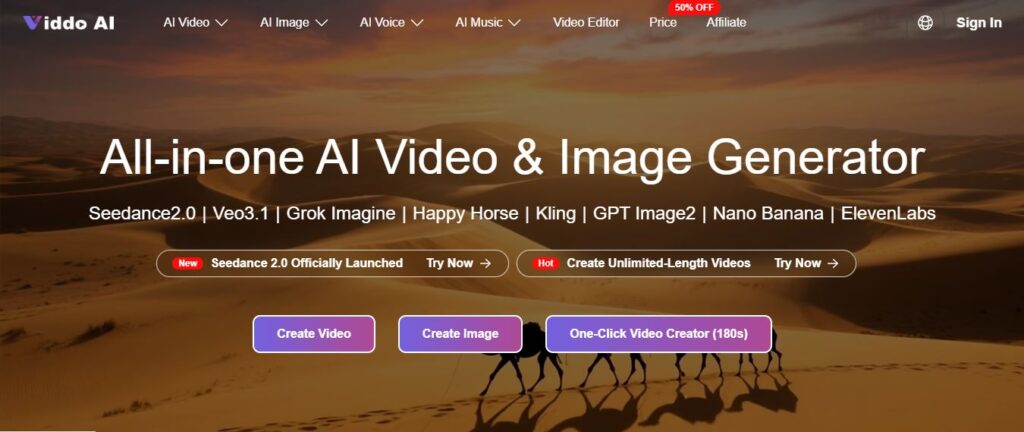
Five Advanced Ways to Use AI Video Generators


